- Main
- Computers - Security
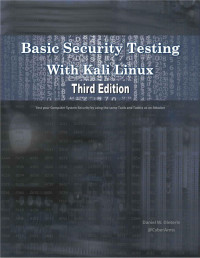
- Basic Security Testing with Kali Linux

Basic Security Testing with Kali Linux
Daniel W. DieterleШҜШ§ Ъ©ШӘШ§ШЁ ШӘШ§ШіЩҲ ШӘЩҮ Ъ…ЩҶЪ«ЩҮ Ш®ЩҲШ§ЪҡЩҮ ШҙЩҲЩҮШҹ
ШҜ ШЁШ§Шұ ШҙЩҲЩҠ ЩҒШ§ЫҢЩ„ Ъ©ЫҢЩҒЫҢШӘ Ъ…ЩҮ ШҜШҰШҹ
ШӘШұ Ъ…ЩҲ ЪҶЫҗ ШҜ Ъ©ШӘШ§ШЁ Ъ©ЫҢЩҒЫҢШӘ ШўШІЩ…Ш§ЫҢЪҡЩҲ ЩҲЪ©Ъ“ШҰШҢ ШЁШ§Шұ ШҰЫҗ Ъ©Ъ“ШҰ
ШҜ ШЁШ§Шұ ШҙЩҲЩҲ ЩҒШ§ЫҢЩ„ЩҲЩҶЩҲ Ъ©ЫҢЩҒЫҢШӘЫҢ Ъ…ЩҮ ШҜШҰШҹ
With computer hacking attacks making headline news on a frequent occasion, it is time for companies and individuals to take a more active stance in securing their computer systems. Kali Linux is an Ethical Hacking platform that allows good guys to use the same tools and techniques that a hacker would use so they can find issues with their security before the bad guys do.
In вҖңBasic Security Testing with Kali LinuxвҖқ, you will learn basic examples of how hackers find out information about your company, locate weaknesses in your security and how they gain access to your system.
This hands-on, step by step learning book covers topics like:
Kali Linux Introduction and Overview
Metasploit & Metasploitable 2 Tutorials
Information Gathering
A section on Shodan (the вҖңHackerвҖҷs GoogleвҖқ)
Exploiting Windows and Linux Systems
Escalating Privileges in Windows
Wireless (WiFi) Attacks
Social Engineering Attacks
Password Attacks
Kali on a Raspberry Pi
Securing your Network
Though no network can be completely вҖңHacker ProofвҖқ, knowing how an attacker works will help put you on the right track of better securing your network.
In вҖңBasic Security Testing with Kali LinuxвҖқ, you will learn basic examples of how hackers find out information about your company, locate weaknesses in your security and how they gain access to your system.
This hands-on, step by step learning book covers topics like:
Kali Linux Introduction and Overview
Metasploit & Metasploitable 2 Tutorials
Information Gathering
A section on Shodan (the вҖңHackerвҖҷs GoogleвҖқ)
Exploiting Windows and Linux Systems
Escalating Privileges in Windows
Wireless (WiFi) Attacks
Social Engineering Attacks
Password Attacks
Kali on a Raspberry Pi
Securing your Network
Though no network can be completely вҖңHacker ProofвҖқ, knowing how an attacker works will help put you on the right track of better securing your network.
ШҜШұШ¬ЩҮ (ЩӮШ§Ш·ЫҢШәЩҲШұЫҢ(:
Ъ©Ш§Щ„:
2013
Ш®ЩҫШұЩҶШҜЩҲЫҢЩҮ Ш§ШҜШ§ШұЩҮ:
CreateSpace
ЪҳШЁЩҮ:
english
ШөЩҒШӯЩҮ:
242
ISBN 10:
1494861275
ISBN 13:
9781494861278
ЩҒШ§ЫҢЩ„:
PDF, 13.77 MB
ШіШӘШ§ШіЫҢ ШӘЫҢЪ«ЫҢ:
IPFS:
CID , CID Blake2b
english, 2013
ЩҫЩҮ ШўЩҶ Щ„Ш§ЫҢЩҶ ЪүЩҲЩ„ Щ„ЩҲШіШӘЩ„
- Ъ©Ш§ЩҫЫҢ Ъ©ЩҲЩ„
- pdf 13.77 MB Current page
- Checking other formats...
- ШӘЩҮ ШЁШҜЩ„ЩҲЩ„
- Unlock conversion of files larger than 8 MBPremium
ШәЩҲШ§Ъ“ШҰ Ъ©ШӘШ§ШЁ ЩҫЩ„ЩҲШұЩҶЪҒЩҠ ШӘЩҮ Ш§Ш¶Ш§ЩҒЩҮ ЩҲЪ©Ъ“ШҰШҹ Щ…ЩҲЩҶЪ– ШіШұЩҮ ШҜ support@z-lib.do Щ„ЩҮ Щ„Ш§ШұЫҗ Ш§Ъ“ЫҢЪ©ЩҮ ЩҲЩҶЫҢШіШҰ
ШҜ Ыұ- Ыө ШҜЩӮЫҢЩӮЩҲ ЩҫЩҮ Ш¬ШұЫҢШ§ЩҶ Ъ©Ыҗ ЩҒШ§ЫҢЩ„ ШіШӘШ§ШіЫҢ Ш§ЫҢЩ…Щ„ ШӘЩҮ ШҜШұШұШіЫҢЪ–ЫҢ.
ШҜ Ыұ-Ыө ШҜЩӮЫҢЩӮЩҲ ЩҫЩҮ ШӘШұЪ… Ъ©ЪҡЫҗ ШЁЩҮ ЩҒШ§ЫҢЩ„ ШіШӘШ§ШіЩҲ ШҜ ЩјЫҢЩ„ЫҢЪ«ШұШ§Щ… ШўЪ©Ш§ЩҲЩҶЩј ШӘЩҮ ЩҲШіЩҫШ§ШұЩ„ ШҙЩҠ.
ЫҢШ§ШҜЩҲЩҶЩҮ: Щ…Ш·Щ…ШҰЩҶ ШҙШҰ ЪҶЫҗ ШӘШ§ШіЩҲ Ш®ЩҫЩ„ ШўЪ«Ш§ЩҲЩҶЩј ШҜ Z-Library Telegram ШЁЩҲЩј ШіШұЩҮ ШӘЪ“Щ„ЫҢ ШҜЫҢ.
ШҜ Ыұ-Ыө ШҜЩӮЫҢЩӮЩҲ ЩҫЩҮ ШӘШұЪ… Ъ©ЪҡЫҗ ШЁЩҮ ЩҒШ§ЫҢЩ„ ШіШӘШ§ШіЩҲ ШҜ Kindle ЩҲШіЫҢЩ„Ыҗ ШӘЩҮ ЩҲШіЩҫШ§ШұЩ„ ШҙЩҠ.
Щ…Щ„Ш§ШӯШёЩҮ ЩҮШұ Ъ©ШӘШ§ШЁ ЪҶЩҠ ШӘШ§ШіЩҠ Kindle ШӘЩҮ Щ„ЩҠЪ–ШҰ ШЁШ§ЫҢШҜ ШӘШөШҜЫҢЩӮ ШҙЫҢ. Ш®ЩҫЩ„ЩҮ Ш§Щ„Ъ©ШӘШұЩҲЩҶЫҢЪ©ЫҢ ЩҫЩҲШіШӘЩҮ ШӘЩҒШӘЫҢШҙ Ъ©Ъ“ШҰ ЪҶЫҗ ЩҫЪ©ЪҡЫҗ ШЁШ§ЫҢШҜ ШҜ Amazon Kindle Support Щ„ЩҮ Ш®ЩҲШ§ Щ…Ъ©ШӘЩҲШЁ ЩҲЫҢ.
ШӘЩҮ ШЁШҜЩ„ЩҲЩҶ ЩҫЩҮ Ъ©Ш§Шұ ШҜЩҠ
ШӘЩҮ ШЁШҜЩ„ЩҲЩҶ ЩҶШ§Ъ©Ш§Щ… ШҙЩҲ
Premium benefits
- Send to eReaders
- Increased download limit
 File converter
File converter ШҜ Щ„ЩјЩҲЩҶ ЩҶЩҲШұЫҗ ЩҶШЁЫҢШ¬Ыҗ
ШҜ Щ„ЩјЩҲЩҶ ЩҶЩҲШұЫҗ ЩҶШЁЫҢШ¬Ыҗ More benefits
More benefits
Щ…ЩҮЩ…ЩҠ Ш¬Щ…Щ„ЩҠ
ШҜ Ъ©ШӘШ§ШЁЩҲЩҶЩҲ Щ…ШұШӘШЁШ· Щ„ЫҢШіЩјЩҲЩҶЩҮ







































































































































 Amazon
Amazon  Barnes & Noble
Barnes & Noble  Bookshop.org
Bookshop.org 

![Jack Mathew [Mathew, Jack] — Hacking with Kali Linux: A Complete Guide for Beginners to Study Basic Hacking, Cybersecurity, Wireless Networks, and Penetration Testing](https://s3proxy.cdn-zlib.se/covers200/collections/userbooks/19b770da0fd91d1c524c1986de41186c2485c58dbe87c8ac8bfc56c21f7b7535.jpg)

![Alan T. Norman [Norman, Alan T.] — Computer Hacking Beginners Guide: How to Hack Wireless Network, Basic Security and Penetration Testing, Kali Linux, Your First Hack](https://s3proxy.cdn-zlib.se/covers200/collections/userbooks/cc48d21f209751861d39d06d7c05a51e60a5418ea58e417d74bbf77c06a46341.jpg)


![Daniel Dieterle [Dieterle, Daniel] — Intermediate Security Testing with Kali Linux 2](https://s3proxy.cdn-zlib.se/covers200/collections/userbooks/28cb970963248cac580c17ded428715176866474605f278e733f9dfd04ba9660.jpg)